MANTEC: Strengthening South Central Pennsylvania Manufacturing Every manufacturing operation has them: the skilled machinist promoted…

Manufacturing companies face unprecedented scrutiny under International Traffic in Arms Regulations (ITAR), with violations carrying penalties reaching $1.3 million per incident and potential criminal charges. Recent enforcement actions by the State Department’s Directorate of Defense Trade Controls show a 40% increase in investigations, making compliance more critical than ever for defense contractors and manufacturers handling controlled articles.
One misstep can halt global shipments, freeze operations, and damage customer relationships permanently. Companies like Raytheon and General Electric have faced multi-million dollar penalties for ITAR violations, proving that even industry giants aren’t immune to enforcement actions. The complexity of modern supply chains and evolving regulatory requirements make self-assessment a critical defense strategy for protecting your business.
MANTEC’s ITAR compliance consulting services help manufacturers manage these complex regulations through comprehensive audits, training programs, and ongoing support. A thorough self-audit serves as your first line of defense against costly violations and regulatory action.
How to Use This Self-Audit Checklist
This comprehensive checklist provides a systematic approach to evaluating your ITAR compliance status across seven critical areas. Each section includes specific criteria that determine pass or fail status for your organization.
Start by assembling a cross-functional team including representatives from quality, security, IT, legal, and operations. Document all findings with specific evidence and dates. Score each section as either “Pass” or “Fail” based on the criteria provided.
Create a remediation plan for any failed sections, prioritizing areas with the highest risk exposure. Schedule quarterly reviews to maintain compliance status and track improvement progress. This structured approach helps identify gaps before they become violations.
Pass/Fail Criteria by Section
Controlled Articles Inventory and Marking
Pass Criteria:
- Complete inventory of all ITAR-controlled articles maintained with accurate part numbers and descriptions
- Physical marking requirements met on all applicable items with proper ITAR notices
- Storage areas clearly designated and restricted to authorized personnel only
- Inventory reconciliation performed monthly with documented variance investigations
Fail Criteria:
- Missing or incomplete inventory records for controlled articles
- Unmarked items that require ITAR designation under regulations
- Controlled articles stored in unrestricted areas accessible to unauthorized personnel
- Inventory discrepancies without proper investigation and documentation
Track serial numbers, locations, and custody transfers for all controlled items. Implement barcoding systems where possible to reduce human error. Regular physical counts prevent inventory drift that often triggers regulatory concerns.
Export License Documentation
Pass Criteria:
- Current export licenses maintained for all applicable transactions with proper authorization limits
- Complete transaction records showing license compliance for each shipment
- Automated systems in place to prevent shipments exceeding license parameters
- Regular license renewal tracking with advance planning for expiration dates
Fail Criteria:
- Expired or missing export licenses for controlled transactions
- Shipments that exceed license quantity or value limitations
- Incomplete documentation for export transactions or missing required forms
- No systematic tracking of license utilization or renewal requirements
Establish digital workflows that automatically flag license expiration dates 90 days in advance. Maintain backup documentation for all export transactions in both physical and electronic formats. Cross-reference every shipment against current license parameters before release.
ITAR Training and Record-Keeping
Pass Criteria:
- Annual ITAR training completed by all personnel handling controlled information or articles
- Training records maintained for minimum three-year retention period with completion certificates
- Role-specific training provided based on individual access levels and responsibilities
- New employee training completed within 30 days of hire for positions requiring ITAR access
Fail Criteria:
- Personnel handling controlled items without current ITAR training certification
- Missing or incomplete training records for employees with ITAR responsibilities
- Generic training that doesn’t address specific job functions or access levels
- New employees granted ITAR access before completing required training programs
Develop customized training modules that address specific job functions rather than generic compliance overviews. Track training effectiveness through periodic assessments and refresher sessions. Document all training activities with signed acknowledgment forms and test results.
Physical Security and Access Controls
Pass Criteria:
- Restricted access controls implemented for all areas containing controlled articles or information
- Badge reader systems or equivalent tracking all entries and exits to controlled areas
- Visitor escort procedures enforced with proper documentation and background verification
- Security incident reporting system in place with timely investigation protocols
Fail Criteria:
- Unrestricted access to areas containing ITAR-controlled materials or information
- Visitors granted unescorted access to controlled areas without proper authorization
- Missing or inadequate physical barriers separating controlled from non-controlled areas
- Security incidents not properly documented or investigated according to established procedures
Install card reader systems that create audit trails for all access events. Establish clear procedures for visitor management including background checks and escort requirements. Regular security assessments help identify potential vulnerabilities before they become compliance issues.
Technology Control Plan (TCP) Enforcement
Pass Criteria:
- Written Technology Control Plan addressing all controlled technologies and technical data
- Regular plan updates reflecting changes in technology scope or personnel access
- Clear procedures for technology release approval with documented authorization chains
- Employee acknowledgment of TCP requirements with signed compliance agreements
Fail Criteria:
- Missing or outdated Technology Control Plan that doesn’t reflect current operations
- Unauthorized technology transfers or releases without proper approval documentation
- Personnel accessing controlled technology without appropriate clearance or need-to-know basis
- TCP violations not properly investigated or remediated according to established procedures
Review and update your TCP quarterly to reflect organizational changes and new technology acquisitions. Establish clear approval workflows for technology releases with multiple authorization levels. Train personnel on TCP requirements specific to their roles and responsibilities.
Cybersecurity and Data Protection Measures
Pass Criteria:
- Network segmentation implemented to isolate systems containing controlled technical data
- Multi-factor authentication required for all systems accessing ITAR-controlled information
- Regular cybersecurity assessments performed with documented remediation of identified vulnerabilities
- Incident response plan in place with specific procedures for ITAR-related data breaches
Fail Criteria:
- ITAR-controlled data accessible through unsecured network connections or systems
- Single-factor authentication used for systems containing controlled technical information
- Missing or outdated cybersecurity controls that don’t meet current threat landscape requirements
- No documented incident response procedures for potential ITAR data compromises
Implement network monitoring tools that provide real-time visibility into data access and transfer activities. Regular penetration testing helps identify vulnerabilities before malicious actors exploit them. Establish encrypted communication channels for all ITAR-related data transmission.
Restricted Party Screening Processes
Pass Criteria:
- Automated screening systems check all parties against current restricted lists before engagement
- Regular database updates ensure screening against most current restricted party information
- Documented procedures for handling potential matches with proper escalation protocols
- Periodic re-screening of existing business partners and employees with ITAR access
Fail Criteria:
- Manual screening processes that may miss restricted party updates or create gaps
- Outdated screening databases that don’t reflect current restricted party list changes
- Business relationships established without proper restricted party screening documentation
- No ongoing monitoring of business partners for potential restricted party list additions
Subscribe to automated restricted party screening services that provide real-time updates when new entities are added to watch lists. Establish procedures for immediate suspension of business activities when potential matches are identified. Regular auditing of screening processes helps ensure consistent application across all business relationships.
Remediation Tips for Failed Sections
When your audit identifies failed sections, prioritize remediation based on regulatory risk and business impact. Start with areas that could result in immediate export violations or criminal liability.
Create standardized templates for common compliance documents including Technology Control Plans, visitor logs, and training records. These templates ensure consistency and reduce the time required for documentation updates.
Establish clear timelines for remediation activities with specific milestones and responsible parties. Regular progress reviews help maintain momentum and identify obstacles that require additional resources or support.
Consider implementing automated compliance monitoring tools that provide real-time alerts when activities approach regulatory limits or requirements. These systems help prevent violations rather than just detecting them after occurrence.
For complex remediation projects, cybersecurity and compliance programs can provide additional expertise and resources. Professional guidance helps address remediation efforts that focus on root causes rather than just immediate symptoms.
Next Steps After Your Audit
Self-audits provide valuable insights, but professional validation adds credibility and thoroughness to your compliance program. Engage certified ITAR consultants to review your self-assessment findings and provide independent verification of compliance status.
Schedule follow-up audits every six months to maintain compliance momentum and catch emerging issues before they become violations. Regular assessment cycles help embed compliance thinking into daily operations rather than treating it as an annual activity.
Develop key performance indicators that track compliance effectiveness over time. Metrics like training completion rates, security incident frequency, and audit finding resolution time provide objective measures of program improvement.
Consider implementing manufacturing cybersecurity best practices that complement ITAR requirements. Strong cybersecurity foundations support ITAR compliance and protect against broader business risks.
Document lessons learned from each audit cycle and share findings across your organization. Building institutional knowledge helps prevent recurring issues and improves overall compliance culture.
Building Long-Term Compliance Success
Successful ITAR compliance requires sustained commitment rather than periodic compliance checks. Embed compliance requirements into standard operating procedures so they become part of normal business processes.
Establish clear communication channels between compliance, operations, and leadership teams. Regular reporting helps ensure compliance issues receive appropriate attention and resources for resolution.
Invest in employee development programs that build compliance expertise within your organization. Internal subject matter experts reduce dependency on external consultants while improving day-to-day compliance execution.
Consider joining industry associations and compliance forums where you can learn from peer experiences and stay current on regulatory developments. Collaborative learning helps identify best practices and avoid common pitfalls.
Regular benchmarking against industry standards helps ensure your compliance program remains effective as regulations and business requirements evolve. Continuous improvement prevents compliance drift that can lead to violations.
Technology Solutions for Compliance Management
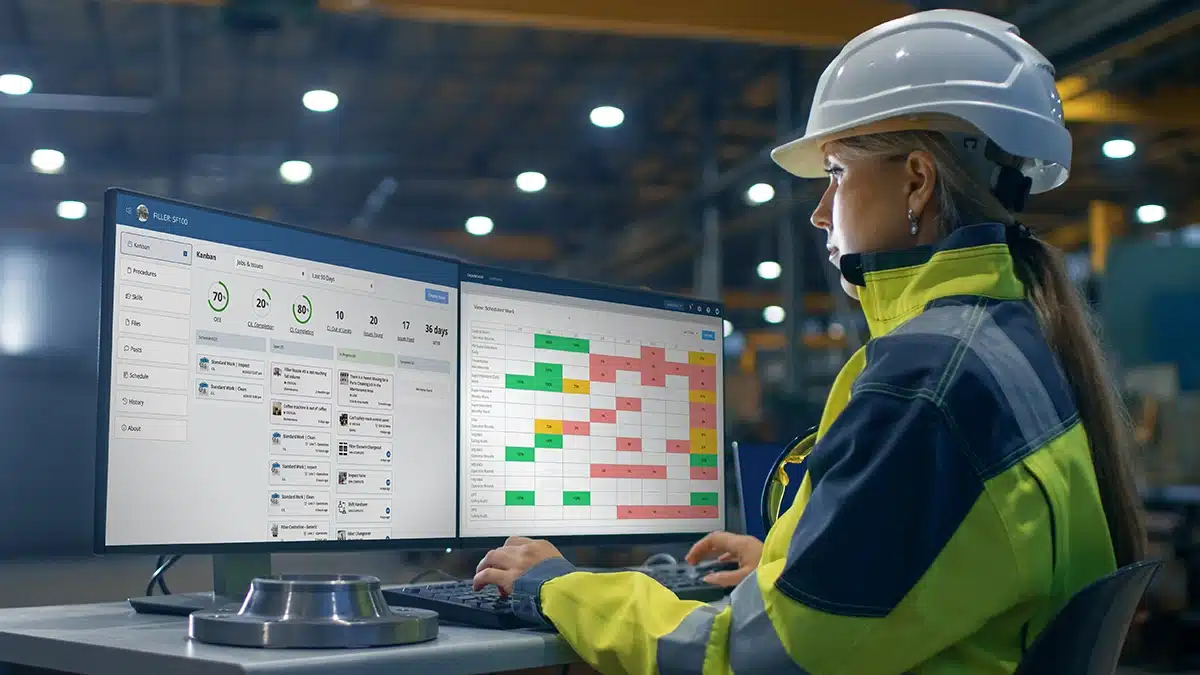
Modern compliance management software can automate many routine ITAR requirements including license tracking, training management, and restricted party screening. These tools reduce manual errors while providing audit trails for regulatory purposes.
Cloud-based solutions offer scalability and accessibility benefits but require careful evaluation of data security and sovereignty requirements. ITAR-controlled technical data has specific restrictions on cloud storage and processing locations.
Integration between compliance tools and existing business systems eliminates data silos and reduces duplicate data entry requirements. Seamless workflows improve compliance efficiency while reducing the burden on operational staff.
Mobile applications can extend compliance capabilities to field operations and remote workers. Real-time access to compliance information helps prevent violations during customer visits and off-site activities.
Regular system audits ensure compliance tools continue meeting regulatory requirements as both technology and regulations evolve. Technology solutions should enhance rather than complicate compliance activities.
Measuring Compliance Program Effectiveness
Establish baseline metrics for your current compliance status before implementing improvement initiatives. Quantitative measures help demonstrate program value and identify areas requiring additional focus.
Track leading indicators like training completion rates and audit finding closure times rather than just lagging indicators like violation incidents. Proactive metrics help prevent problems rather than just measuring their occurrence.
Regular stakeholder feedback provides qualitative insights into compliance program effectiveness and user satisfaction. Employee input helps identify friction points that could undermine compliance efforts.
Benchmark your program against industry best practices and peer organizations when possible. External perspective helps identify improvement opportunities and validate current approaches.
Document program improvements and their business impact to build support for continued compliance investment. Demonstrating value helps ensure compliance receives adequate resources and organizational priority.
Crisis Management and Violation Response
Develop comprehensive incident response procedures that address potential ITAR violations before they occur. Clear escalation protocols help ensure appropriate leadership involvement and timely regulatory notification when required.
Establish relationships with specialized legal counsel who understand ITAR requirements and enforcement practices. Having pre-existing relationships reduces response time when urgent legal guidance is needed.
Create communication protocols that balance transparency with legal privilege considerations. Proper documentation helps demonstrate good faith compliance efforts while protecting attorney-client privilege when appropriate.
Regular tabletop exercises help test incident response procedures and identify gaps in crisis management capabilities. Practice scenarios should include various violation types and severity levels.
Post-incident analysis helps identify root causes and prevent recurrence of similar issues. Learning from compliance failures strengthens overall program effectiveness and demonstrates commitment to continuous improvement.
Ready to strengthen your ITAR compliance program and protect your business from costly violations? Schedule your complimentary ITAR consultation with MANTEC’s compliance experts today. Our experienced team will review your current program, identify improvement opportunities, and develop a customized action plan for achieving sustained compliance success.
Industry Standards and Compliance Resources
The Directorate of Defense Trade Controls provides comprehensive guidance on ITAR implementation through their official publications and policy updates. Visit the State Department’s DDTC website for access to current regulations, policy statements, and compliance guidance documents that form the foundation of effective ITAR programs.
The National Institute of Standards and Technology offers cybersecurity frameworks that complement ITAR requirements for protecting controlled technical data. Review NIST cybersecurity guidance to understand how industry-standard security controls support ITAR compliance objectives while strengthening overall organizational cybersecurity posture.
Frequently Asked Questions
How often should we conduct ITAR self-audits? Conduct comprehensive self-audits quarterly, with monthly spot checks on high-risk areas like export license utilization and restricted party screening. This frequency helps catch issues early while maintaining compliance momentum. Annual third-party audits provide additional validation and external perspective on your compliance program effectiveness.
What documentation is required for ITAR compliance audits? Maintain comprehensive records including export license applications and approvals, technology control plans, employee training certificates, visitor logs, and restricted party screening results. Document retention requirements extend for five years minimum, with some records requiring permanent retention. Digital document management systems help organize and protect these critical compliance records.
Can small manufacturers afford professional ITAR compliance consulting? Professional ITAR consulting represents a fraction of potential violation penalties and provides risk mitigation that protects business continuity. Many consultants offer scalable services tailored to small manufacturer budgets and needs. The cost of prevention through professional guidance is significantly lower than the cost of violations or lost business opportunities.
How do we handle ITAR compliance for remote workers? Remote work requires additional security controls including secure VPN connections, endpoint protection software, and physical security measures for home offices. Technology control plans must address remote access scenarios with specific approval and monitoring procedures. Regular training helps remote workers understand their compliance responsibilities and reporting requirements.
What should we do if we discover a potential ITAR violation? Immediately cease the activity in question and conduct a thorough investigation to determine the scope and impact of the potential violation. Contact specialized legal counsel for guidance on disclosure requirements and remediation steps. Document all investigation activities and corrective actions taken to demonstrate good faith compliance efforts and organizational commitment to regulatory adherence.